- Install the Docker image and start the container
- Add Ssl Certificate To Windows Docker Container
- Add Ssl Certificate To Docker Container Tracking
- Add Ssl Certificate To Docker Container Search
The Apache HTTP Server Project. Canister.io — 20 free private repositories for developers, 30 free private repositories for teams to build and store Docker images; Container Registry Service - Harbor based Container Management Solution. Free tier offers 1 GB storage for private repositories. Storage customization Customize the storage location. By default, your registry data is persisted as a docker volume on the host filesystem. If you want to store your registry contents at a specific location on your host filesystem, such as if you have an SSD or SAN mounted into a particular directory, you might decide to use a bind mount instead. Exit the container if you haven't already, then use the docker command to restart the container: docker restart netdata. Host-editable configuration # If you want to make your container's configuration directory accessible from the host system, you need to use a volume rather than a bind mount.
This is how you can run GitLab Runner inside a Docker container.
General GitLab Runner Docker image usage
GitLab Runner Docker images (based on Ubuntu or Alpine Linux)are designed as wrappers around the standard gitlab-runner command, like ifGitLab Runner was installed directly on the host.
The general rule is that every GitLab Runner command that normally would be executedas:
can be executed with:
For example, getting the top-level help information for GitLab Runner command could beexecuted as:
In short, the gitlab-runner part of the command is replaced withdocker run [docker options] gitlab/gitlab-runner, while the rest of thecommand stays as it is described in the register documentation.The only difference is that the gitlab-runner command is executed inside of aDocker container.
Install the Docker image and start the container
Before you begin, ensure Docker is installed.
To run gitlab-runner inside a Docker container, you need to make sure that the configuration is not lost when the container is restarted. To do this, there are two options, which are described below.
Add Ssl Certificate To Windows Docker Container
Make sure that you read the FAQ section which describes some of the most common problems with GitLab Runner.
session_server, you will also need to expose port 8093 by adding -p 8093:8093 to your docker run command.Option 1: Use local system volume mounts to start the Runner container
This example uses the local system for the configuration volume that is mounted into the gitlab-runner container. This volume is used for configs and other resources.
Option 2: Use Docker volumes to start the Runner container
In this example, you can use a configuration container to mount your custom data volume.
Create the Docker volume:
Start the GitLab Runner container using the volume we just created:
docker run command, use the flag --env TZ=<TIMEZONE>. View a list of available time zones.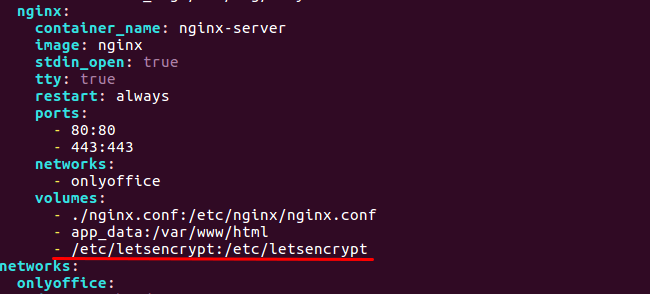
Register the runner
The final step is to register a new runner. The GitLab Runner Container won’t pick up any jobs until it’s registered.
Update configuration
If you change the configuration in config.toml, you might need to restart the runner to apply the change.Make sure to restart the whole container instead of using gitlab-runner restart:
Upgrade version
Pull the latest version (or a specific tag):
Stop and remove the existing container:
Start the container as you did originally:
-v /srv/gitlab-runner/config:/etc/gitlab-runner or--volumes-from gitlab-runner-config).Reading GitLab Runner logs
When GitLab Runner is started as a foreground task (whether it’s a locally installed binary orinside of a Docker Container), the logs are printed to the standard output. WhenGitLab Runner is started as a system service (e.g. with Systemd), the logs are in mostcases logged through Syslog or other system logging mechanism.
With GitLab Runner started as a Docker based service, since the gitlab-runner ... command isthe main process of the container, the logs can be read using the docker logs command.
For example, if GitLab Runner was started with the following command:
you may get the logs with:
where gitlab-runner is the name of the container, set with --name gitlab-runner bythe first command.
You may find more information about handling container logs at the Docker documentationpage.
Installing trusted SSL server certificates
If your GitLab CI server is using self-signed SSL certificates then you shouldmake sure the GitLab CI server certificate is trusted by the GitLab Runnercontainer for them to be able to talk to each other.
The gitlab/gitlab-runner image is configured to look for the trusted SSLcertificates at /etc/gitlab-runner/certs/ca.crt, this can however be changed using the-e 'CA_CERTIFICATES_PATH=/DIR/CERT' configuration option.
Copy the ca.crt file into the certs directory on the data volume (or container).The ca.crt file should contain the root certificates of all the servers youwant GitLab Runner to trust. The GitLab Runner container willimport the ca.crt file on startup so if your container is already running youmay need to restart it for the changes to take effect.
Docker images
The following multi-platform Docker images are available:
gitlab/gitlab-runner:latestbased on Ubuntu.gitlab/gitlab-runner:alpinebased on Alpine with much a smaller footprint(~160/350 MB Ubuntu vs ~45/130 MB Alpine compressed/decompressed).
See GitLab Runnersource for possible build instructions for both Ubuntu and Alpine images.
docker-machine dependency, as it is not yet maintained for the Linux s390xplatform. See issue for current status.SELinux
Some distributions (CentOS, RedHat, Fedora) use SELinux by default to enhance the security of the underlying system.
Special care must be taken when dealing with such a configuration.
- If you want to use the Docker executor to run builds in containers, you’ll need access to
/var/run/docker.sock.However, if SELinux is in enforcing mode, you will see aPermission deniederror when you’re accessing/var/run/docker.sock.Install selinux-dockersock to resolve this issue. - Make sure that a persistent directory is created on host:
mkdir -p /srv/gitlab-runner/config. - Run Docker with
:Zon volumes:
More information about the cause and resolution can be found here:http://www.projectatomic.io/blog/2015/06/using-volumes-with-docker-can-cause-problems-with-selinux/
Help & feedback
Docs
Edit this pageto fix an error or add an improvement in a merge request.Create an issueto suggest an improvement to this page.
Show and post commentsto review and give feedback about this page.
Product
Create an issueif there's something you don't like about this feature.Propose functionalityby submitting a feature request.
Join First Lookto help shape new features.
Feature availability and product trials
View pricingto see all GitLab tiers and features, or to upgrade.Try GitLab for freewith access to all features for 30 days.
Get Help
If you didn't find what you were looking for,search the docs.
If you want help with something specific and could use community support,post on the GitLab forum.
For problems setting up or using this feature (depending on your GitLabsubscription).
Add Ssl Certificate To Docker Container Tracking
Request supportAdd Ssl Certificate To Docker Container Search
Please enable JavaScript to view thecomments powered by Disqus.